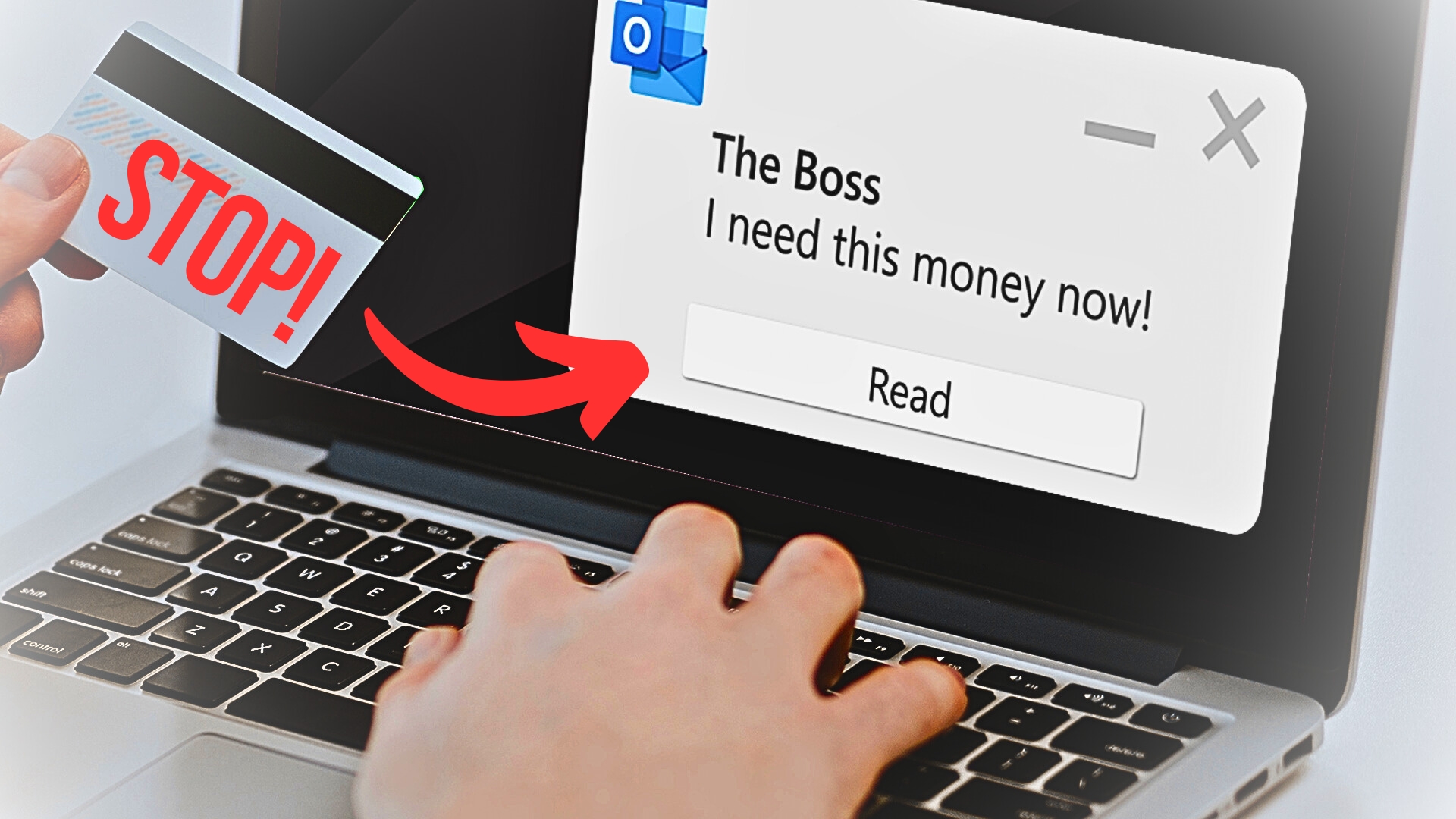
How many times a day do you respond to an email without really thinking about its contents?
Maybe it’s a request for some information. Perhaps it’s asking you to pay an invoice. All mundane stuff. But no sooner than you’ve hit send, you’ve fallen victim to a Business Email Compromise (BEC) attack.
A business email compromise (BEC) assault occurs when a cyber criminal acquires access to your business email account and utilizes it to deceive your employees, clients, or partners into sending them money or sensitive information. They accomplish this by imitating a senior official and exploiting their position of trust.
It may appear that this is something that only happens to large organizations, but this is not the case.
Small and medium-sized firms, according to the FBI, are just as vulnerable to BEC assaults as larger ones. In reality, over the last several years, these attacks have cost corporations more than £20 billion.
And Microsoft provides more bad news, revealing that they’re becoming both more harmful and more difficult to detect.
So, what can you do to protect your business from BEC attacks? Here’s our advice:
1. Educate your employees: They are the first line of defence against BEC attacks. They need to know how to spot phishing emails, suspicious requests, and fake invoices. Train them regularly on cybersecurity best practice, like strong passwords, multifactor authentication, and secure file sharing.
2. Use advanced email security solutions: Basic email protections like antispam and antivirus software are no longer enough to block BEC attacks. You need more advanced solutions that use artificial intelligence and machine learning to detect and prevent these attacks in real-time. Look for email security providers that offer features like domain-based message authentication, reporting, and conformance (DMARC), sender policy framework (SPF), and DomainKeys Identified Mail (DKIM).
3. Set up transaction verification procedures: Before transferring funds or sensitive information, establish a verification process that confirms the authenticity of the request. This could include a phone call, video conference, or face-to-face meeting. Don’t rely on email alone to confirm these types of requests.
4. Monitor your email traffic: Regularly monitor your email traffic for anomalies and unusual patterns. Look for signs like unknown senders, unusual login locations, changes to email settings or forwarding rules, and unexpected emails. Make sure you have a clear protocol in place for reporting and responding to any suspicious activity.
5. Keep your software up to date: Ensure that you’re always running the latest version of your operating system, email software, and other software applications. These updates often include vital security patches that address known vulnerabilities.
BEC assaults are growing more widespread and complex, but you can defend your business with the correct awareness, training, and security solutions.
Don’t wait until it’s too late; take action now to protect your company.
If you want to learn more about how to defend your company against cyberattacks, our team is always available to assist you. Contact us today.